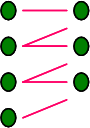
 The Task Group on access management from the NISO Metasearch Intiative – chaired by my colleague Mike Teets – has made a very useful report [pdf] available. This provides a framework within which to examine existing authentication and authorization methods, and describes those methods. It encapsulates nicely current understanding of issues and approaches.
The Task Group on access management from the NISO Metasearch Intiative – chaired by my colleague Mike Teets – has made a very useful report [pdf] available. This provides a framework within which to examine existing authentication and authorization methods, and describes those methods. It encapsulates nicely current understanding of issues and approaches.
Within the academic community, Shibboleth is the subject of much discussion. I sometimes wonder, though, if in a few years time we will be using something that emerges within the social networking space where identity management has become an issue given, among other things, the hassle caused by comment and trackback spam.
Share
More from LorcanDempsey.net